Locked Away — HackTheBox
Difficulty: Very Easy
Introduction
This is a python challenge hosted on HTB network... you're given an IP address with a TCP port and downloadable files that contain a flag.txt file and main.py file.
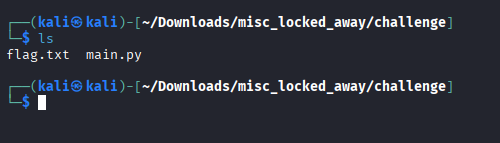
First I find it useful or necessary to cat out the flag just to see if it's actually real or simply a troll, I also like to ls -la the downloaded files as people sometimes hide their flags.
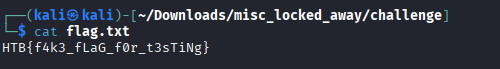
Obviously it was a fake flag so the next step is to dive into the challenge and see what we're working with when it comes to the python script.
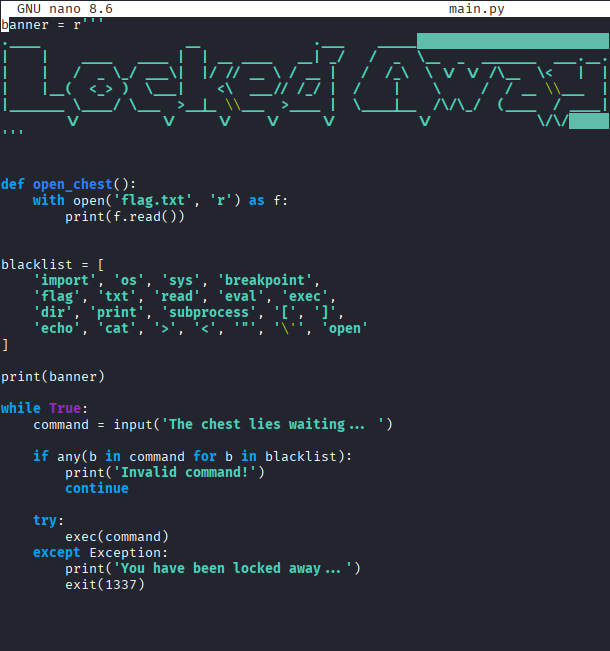
Script Analysisprize
open_chest()function:- This is the end goal, it'll output the contents of
flag.txt
- This is the end goal, it'll output the contents of
blacklist:- Contains a list of 'banned' substrings (`import, os, flag, open)
banner:- Simply ASCII art displayed at the startup to make this challenge cool (always do it for the vibe factor)
Basically any input that gets evaluated by the exec(command) function will just repeat the The chest lies waiting... string until you find a valid way to pull the flag... simply a puzzle box kind of challenge but within the realm of Python.
Initial thought process was what can I do to clear the list.
blacklist = [] wouldn't work because my input contained [ and ].
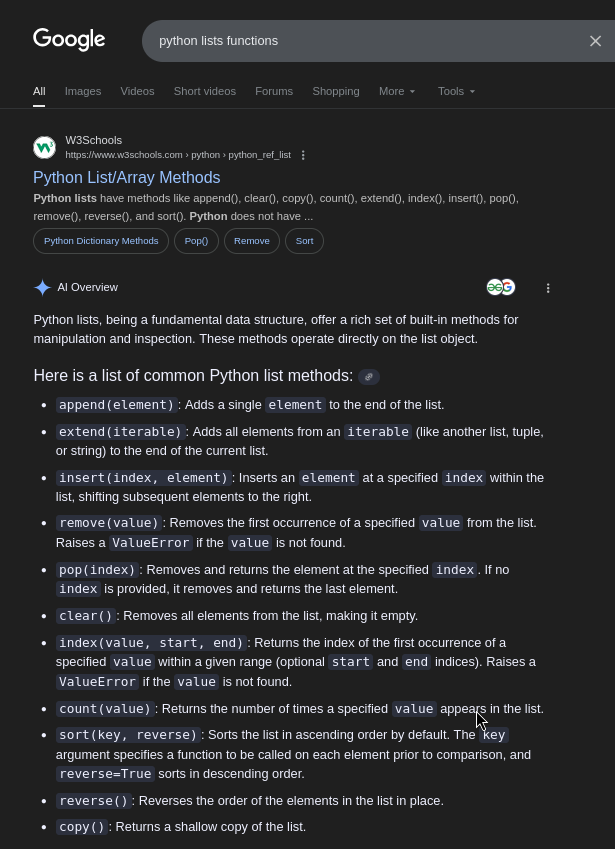
However, I decided on that note let me refresh my knowledge on lists in Python.
I don't condone excessive use of AI in-fact if you'd like to google dork away the AI Overview feature google has, you can simply use the -ai tag in your search.
However, immediately realized the clear() function was going to be knight in shinning armor for this challenge.
blacklist.clear()
Boom that's immediately taken the blacklist = [etc. etc.] and cleared it to blacklist=[] as my initial approach was.
After clearing the list of any values you can run the beautiful open_chest() function to collect your flag.
nc IP-Address PortSimple netcat connection to interact with the script allows us to follow our tested game plan to perfectly collect our flag.